
21: RUSHING THROUGH (SKIPPING, Do It In Hurry): (A) Perform harmful and hazardous operations at a very high speed or (B) perform an action for a very short duration or skip a part or phase or stage or step to eliminate or reduce the harmful, destructive, negative or hazardous effect on the object (or system) or its environment
EXAMPLE: Flash Photography, Laser Eye Correction, Explosive Excavation, High Speed Drills (to avoid heating of surfaces), Cut plastic faster before it decomposes or disorients or deforms, Laser Bean Cutting, HIgh Speed Dental Drills, Cutting Materials Faster (Avoiding Heat Generation or Distribution).
SYNONYMS: SKIPPING, Do It In Hurry, Pass quickly through difficulty
ACB:
The “Skipping” principle suggests the elimination or skipping of an unnecessary or harmful part of a process, object, or system. This principle encourages the identification of steps, elements, or components that do not contribute to the desired result or may even hinder the effectiveness of the system. In practical terms, applying the “Skipping” principle involves analyzing a process or system to identify any redundant or non-essential elements that can be eliminated without compromising the overall functionality. By skipping unnecessary steps or components, the efficiency and effectiveness of the system can be improved.
Value Stream Mapping (VSM) is a key component of Lean methodology, a philosophy and set of practices aimed at optimizing processes and eliminating waste in order to deliver more value to customers. Lean principles originated from the Toyota Production System and were further developed by Taiichi Ohno, Shigeo Shingo, and others in the mid-20th century. VSM is a visual tool used to analyze and improve the flow of materials and information required to bring a product or service to a customer. It involves (1) Clearly define what value means from the customer’s perspective. (2) Understand and visualize the end-to-end process of delivering value. (3) Eliminate waste (skip or reduce non-value adding activities) and streamline processes to create a smooth flow of work. (4) Respond to customer demand rather than pushing products through the process. (5) Continuously strive for improvement.
VSM helps identify and eliminate various forms of waste (e.g., waiting, overproduction, defects) within a process. By understanding the entire value stream, organizations can optimize the flow of materials and information, reducing lead times and improving efficiency. VSM encourages a focus on delivering value to the customer by aligning processes with customer needs. t provides a basis for continuous improvement efforts, allowing organizations to systematically identify and implement changes. Organizations apply Lean principles and VSM in various industries, including manufacturing, healthcare, and services, to improve efficiency, quality, and customer satisfaction. Lean thinking is not a one-time event but a continuous process of improvement. Lean philosophy, including practices like Value Stream Mapping, aims to create more value for customers by eliminating waste and improving processes, drawing inspiration from the successful practices of the Toyota Production System.
Carnivorous insects with long tongues, such as chameleons, have remarkable abilities to extend and retract their tongues quickly to capture prey. One notable example is the chameleon, which uses its long, specialized tongue for hunting. Chameleons have excellent eyesight and can rotate their eyes independently, allowing them to focus on prey. They spot an insect or other small prey item and aim their eyes and head toward it. The chameleon’s tongue is usually coiled or folded inside its mouth. It readies itself by adjusting its body position and preparing to launch the tongue.
When the chameleon is ready to strike, it rapidly extends its tongue. The tongue is propelled out of the mouth with considerable force. The tongue is sticky at the tip, and as it makes contact with the prey, it adheres to the target. The rapid extension and adhesive nature of the tongue help in securing the prey. Once the prey is captured, the chameleon quickly retracts its tongue. The entire process, from extension to retraction, happens in a fraction of a second. Chameleons are known for their incredibly fast tongue movements. The extension speed can range from about 5 to 8 meters per second (16 to 26 feet per second).
The high speed is facilitated by the stored elastic energy in the collagenous tissues of the tongue. Chameleons have specialized hyoid bones and muscles that act like a catapult, providing the necessary force for rapid tongue projection. The quick extension and retraction of the tongue are crucial for successful prey capture, especially when targeting fast-moving insects. The speed is essential for catching agile and elusive prey. Rapid tongue movement minimizes the chances of the prey escaping or reacting in time. The ability of carnivorous insects, such as chameleons, to extend and retract their tongues quickly is a highly specialized and efficient hunting adaptation. The speed of their tongue movement plays a crucial role in successful prey capture.
A common technology that you may be already knowing is known as an Electronic Toll Collection (ETC) system. Fast Tags are one of the implementations of this technology. Vehicles are equipped with a small RFID (Radio-Frequency Identification) sticker or tag known as a Fast Tag. The Fast Tag contains a unique identification number associated with the vehicle. Toll booths are equipped with RFID readers or scanners positioned overhead or at the toll gate. These readers use radio-frequency signals to communicate with the Fast Tag on approaching vehicles. As a vehicle with a Fast Tag enters the toll booth, the RFID reader reads the tag’s unique ID. The toll amount corresponding to the vehicle’s entry and exit points is automatically deducted from the associated prepaid account or linked bank account. If the vehicle has a valid Fast Tag and sufficient balance, the toll gate barrier opens automatically, allowing the vehicle to pass without stopping. If there’s an issue with the Fast Tag or insufficient balance, an alert is triggered, and the barrier remains closed.
ETC systems eliminate the need for vehicles to stop at toll booths, reducing traffic congestion and improving overall traffic flow. The contradiction addressed is between the need for toll collection and the desire to minimize traffic disruptions. Commuters save time as they can pass through toll booths without stopping, resulting in faster and more efficient journeys. The contradiction resolved here is between toll collection requirements and the desire to minimize its impact i.e. almost by skipping or rushing though the time consumed in this activity. Fast Tags offer a convenient and hassle-free way to pay tolls. Users can recharge their accounts online, and transactions are automatic. The contradiction addressed is also between the need for toll collection and the desire for a convenient and user-friendly process. ETC systems reduce the need for manual cash transactions at toll booths, leading to a more secure and efficient toll collection process. The contradiction here is also between the need for toll collection and the desire to minimize cash handling. Electronic Toll Collection systems like Fast Tags utilize RFID technology to automate toll payments, providing numerous benefits such as reduced traffic congestion, time savings, convenience, and improved toll collection efficiency while addressing various contradictions associated with traditional toll collection methods. In addition to skipping principle, this system also uses prior action as a principles wherein the driver is expected to have loaded the money corresponding to its tag so that the amount gets debited at the time of toll collection.
The emergency call feature on phones, including iPhones, serves as a quick and direct way for users to contact emergency services without having to unlock the device or go through the regular dialing process. This feature is designed for situations where immediate access to emergency services is crucial. When you press the emergency call button (often represented by a phone icon and the word “Emergency” on the lock screen), it triggers a special mode that allows the user to make an emergency call without unlocking the phone. This feature ensures that even if the phone is locked or requires a passcode, users can quickly reach emergency services.
On the lock screen, there is usually a visible option to make an emergency call. Tapping on this option takes the user to a dedicated emergency call interface. The emergency call interface typically allows the user to dial the emergency number (e.g., 911 in the U.S.) without needing to unlock the phone. Users can press the call button, and the call is placed directly to the designated emergency services number. When an emergency call is made, the phone may also automatically provide location information to emergency services. This can assist responders in quickly identifying the caller’s location, especially in situations where the caller may be unable to provide this information verbally.
The primary purpose is to provide users with a quick and straightforward way to contact emergency services in urgent situations. Since emergencies can happen at any time, the feature ensures that access to emergency services is not impeded by a locked phone or forgotten passcode. Some phones, including iPhones, may have additional features like Emergency SOS, which, when activated, can automatically call emergency services and share location information. This is often triggered by pressing a specific button combination. The emergency call feature is a critical safety measure, and its design prioritizes accessibility and speed during emergencies. It’s important for users to be aware of how to use this feature on their specific devices and to only use it in genuine emergency situations. Misuse of emergency services can have serious consequences.
The 2×2 framework of prioritization, often referred to as the Eisenhower Matrix, is a method for categorizing tasks based on their urgency and importance. It was popularized by Dwight D. Eisenhower, the 34th President of the United States and a former general in the U.S. Army. While it is attributed to Eisenhower, the exact origins of the matrix may be debatable. The Eisenhower Matrix consists of four quadrants, each representing a different combination of urgency and importance: Urgent and Important (Do First): Tasks that fall into this quadrant are both urgent and important. They require immediate attention and should be tackled first. These are typically critical tasks or emergencies that demand immediate action. Important, Not Urgent (Schedule): Tasks in this quadrant are important for long-term goals, personal growth, or strategic planning. They are not urgent in the immediate sense, so they can be scheduled and planned for later. This quadrant emphasizes proactive and preventive actions. Urgent, Not Important (Delegate): Tasks in this quadrant are urgent but not necessarily important to you personally. Consider delegating these tasks to others if possible. This allows you to focus on tasks that align with your priorities and responsibilities. Not Urgent and Not Important (Eliminate): Tasks that are neither urgent nor important should be carefully evaluated. They may be distractions or time-wasters. Consider eliminating or minimizing these activities to free up time for more meaningful tasks.
The matrix provides a clear framework for prioritizing tasks based on their urgency and importance, helping individuals focus on what truly matters. By categorizing tasks into quadrants, the matrix aids in effective time management. It encourages individuals to spend more time on tasks that align with their long-term goals and less or no time on tasks that are merely urgent but not essential. The matrix assists in decision-making by providing a visual representation of tasks. It helps individuals make informed choices about where to allocate their time and energy. By addressing urgent and important tasks first, individuals can reduce stress associated with looming deadlines or emergencies. The matrix promotes strategic planning by encouraging individuals to allocate time to tasks that contribute to long-term success and personal growth. Overall, the Eisenhower Matrix is a valuable tool for individuals seeking to manage their time effectively, make informed decisions about task priorities, and strike a balance between short-term urgencies and long-term goals.
Rushing through does not mean one does not do proper planning. There is no hurry or harm when planning. Its the execution of the plan that has to be done quickly and precisely so as to avoid any harmful effect or opposition, thereby making the execution more effective and efficient in its outcomes. Surgical strikes typically refer to military operations that are precise, targeted, and limited in scope, with the intention of causing minimal collateral damage to surrounding areas and infrastructure. These strikes are often carried out with the aim of neutralizing a specific military target or addressing a particular threat. Surgical strikes involve accurate targeting of military assets or specific locations, minimizing the risk of collateral damage to non-military or civilian areas. These operations are usually focused on a specific target or objective, rather than involving large-scale military actions. Surgical strikes are often conducted swiftly, with the element of surprise playing a crucial role in their success. The strikes are designed to achieve well-defined military objectives, such as destroying a terrorist base, neutralizing a high-value target, or disrupting enemy operations.
Advanced military technologies, such as precision-guided munitions and intelligence gathering, are often employed to enhance the precision and effectiveness of surgical strikes. Surgical strikes can be conducted in various military contexts, including counter-terrorism operations, responses to provocations, or efforts to degrade an adversary’s military capabilities. It’s important to note that the term “surgical strikes” is not specific to any one country or military. Different nations may use the term to describe similar operations within their respective military or business or administrative doctrines. The intention behind surgical strikes is to achieve the planned objectives with a focused and proportional use of force, avoiding unmanageable opposition or adverse effects (in many cases if the duration of execution takes a very long time or exposes the strategic focus or the surprise element, its not worth for even consideration for an execution).
Ambulances operate under special rules and regulations to ensure they can quickly and safely reach their destinations, typically hospitals, in emergency situations. Ambulances are equipped with flashing lights and sirens to alert other road users that they are responding to an emergency. When these lights and sirens are activated, it signals that other drivers should yield the right of way to the ambulance. While ambulances have the right to proceed through red lights and stop signs, they are still required to follow traffic rules when possible. They should yield to pedestrians, obey traffic signals when safe, and avoid reckless driving. Other drivers are legally obligated to yield the right of way to an ambulance with activated lights and sirens. Drivers should move to the right and come to a complete stop if necessary, allowing the ambulance to pass safely.
In some areas, ambulances may have access to special lanes or routes to expedite their journey. This can include dedicated emergency lanes on highways or the ability to use certain routes that are not accessible to regular traffic. Ambulances are allowed to proceed through intersections even when traffic signals indicate red, provided they have ensured that it is safe to do so. Other drivers must yield to the ambulance. While ambulances may exceed posted speed limits when responding to emergencies, their speed should still be reasonable and safe given the road conditions. Ambulance crews often maintain communication with their dispatch centers to update them on their location, the status of the patient, and any challenges they may encounter on the route. The primary goal is to reach the patient or medical facility quickly while prioritizing the safety of all road users.
The movement of VIPs (Very Important Persons) or VVIPs (Very Very Important Persons) in a convoy with enhanced security measures is a well-coordinated and planned exercise. Security agencies conduct a thorough risk assessment to identify potential threats and vulnerabilities during the VIP’s movement. Factors such as the VIP’s profile, the route to be taken, the event or purpose of the movement, and the current security situation are considered. Based on the risk assessment, a secure route is selected for the VIP’s convoy. This route is often kept confidential to minimize the risk of security breaches. Alternate routes may also be planned in case of unforeseen circumstances or emergencies. The timings of the VIP’s movement are carefully planned to minimize disruption to regular traffic and ensure a smooth passage. Coordination is established with relevant authorities, including traffic police and local law enforcement, to manage traffic during the movement.
The VIP’s convoy is accompanied by a dedicated security detail, which may include personnel from specialized security forces, intelligence agencies, and local law enforcement. Armored vehicles may be used to enhance security, and the convoy may include multiple vehicles to transport security personnel. Before the VIP’s movement, the route is thoroughly swept for potential security threats (prior action). If need be, sniffer dogs, bomb disposal squads, and security personnel conduct checks to ensure the safety of the route. Traffic police and security personnel are deployed along the route to manage and regulate traffic. Temporary road closures or diversions may be implemented to facilitate the secure movement of the convoy. Effective communication is maintained among the convoy vehicles, security personnel, and command centers. Communication devices such as radios and encrypted communication systems are used to ensure secure and real-time coordination.
The primary purpose is to ensure the safety and security of the VIP or VVIP from potential threats, including terrorist attacks, kidnapping, or other security risks. The planning and coordination aim to minimize disruption to regular traffic while providing a secure and fastest movement for the VIP or VVIP. In case of emergencies or security threats, the convoy is equipped to respond quickly and effectively like even including ambulance to be part of the convoy (cushioning in advance or solution for a probable or anticipated harmful action). The visible presence of a security convoy can act as a deterrent to potential threats, enhancing the VIP’s safety. Overall, the movement of VIPs in a convoy involves meticulous planning, coordination, and security measures to ensure the safety of the individuals involved.
The term “time-saving bias” isn’t a widely recognized cognitive bias by that name, but it can refer to a tendency people may have to prioritize options or decisions that seem to save time in the short term, even if they may not be the most efficient or effective choices in the long run. By addressing time-saving bias and promoting a more balanced approach to decision-making and problem-solving, individuals and organizations can achieve better outcomes and maximize the use of resources over time.
In technical systems or problem-solving contexts, behaviors associated with a “time-saving bias” could include: Quick Fixes: Opting for temporary or quick-fix solutions to problems instead of investing time upfront to address the root cause, which may lead to recurring issues or inefficiencies. Skipping Steps: Skipping steps in a process or workflow in an effort to save time, without considering the potential impact on accuracy, quality, or safety. Ignoring Maintenance: Neglecting regular maintenance or preventive measures in technical systems in order to save time or resources, which may lead to equipment failure or deterioration over time. Short-Term Solutions: Prioritizing solutions that provide immediate time savings or convenience, even if they do not address underlying issues or contribute to long-term improvements. Automating Inefficient Processes: Automating inefficient or poorly designed processes in an attempt to save time, without first optimizing or redesigning the process for efficiency.
To address behaviors associated with a time-saving bias, it’s important to: Consider Long-Term Consequences: Encourage individuals to consider the long-term implications of their decisions and prioritize solutions that provide sustainable benefits over time, even if they require more effort upfront. Promote Efficiency: Provide training and support to help individuals identify and implement more efficient processes, tools, and techniques that balance time savings with quality and effectiveness. Encourage Collaboration: Foster a collaborative environment where individuals can share best practices, learn from each other’s experiences, and collectively identify opportunities for improvement. Emphasize Continuous Improvement: Cultivate a culture of continuous improvement where individuals are encouraged to seek out and implement incremental changes that contribute to long-term efficiency and effectiveness.
The planning fallacy is a cognitive bias in which individuals tend to underestimate the amount of time, resources, or effort required to complete a task or achieve a goal. This bias leads people to be overly optimistic about their abilities and the feasibility of their plans, resulting in deadlines being missed, budgets exceeded, and objectives not fully realized. The planning fallacy can be observed in various contexts, including personal projects, business endeavors, and public infrastructure projects. Some key characteristics of the planning fallacy include: Optimistic estimations: Individuals tend to make overly optimistic predictions about how long it will take to complete a task or project, often failing to account for potential obstacles, delays, or unforeseen complications. Ignoring past experiences: Despite previous instances of similar tasks taking longer than expected, individuals may fail to learn from past experiences and continue to underestimate the time and effort required for future projects. Overconfidence in abilities: People may be overly confident in their own abilities to complete tasks efficiently and effectively, leading them to underestimate the challenges involved and the resources needed. Failure to consider external factors: The planning fallacy often involves a failure to consider external factors, such as dependencies on other people or events, changes in circumstances, or the need for additional resources.
Mitigating the planning fallacy requires taking proactive steps to improve planning and decision-making processes. Some strategies to counteract the effects of the planning fallacy include: Reference class forecasting: Instead of relying solely on optimistic estimates, individuals can use reference class forecasting, which involves comparing the current project to similar past projects to provide a more realistic estimate of time, cost, and resources needed. Breakdown of tasks: Breaking down large tasks or projects into smaller, more manageable components can help individuals identify potential challenges and dependencies, leading to more accurate planning and estimation. Buffering time and resources: Building in buffers of time and resources to account for potential delays, setbacks, and unforeseen circumstances can help mitigate the impact of unexpected obstacles on project timelines and budgets. Regular review and adjustment: Continuously reviewing and adjusting plans based on new information, changing circumstances, and lessons learned from past experiences can help individuals adapt to evolving situations and improve the accuracy of their planning over time. By recognizing and addressing the planning fallacy, individuals and organizations can improve their ability to effectively plan, execute, and complete projects and tasks.
The bike-shedding effect, also known as Parkinson’s Law of Triviality, is a concept that highlights the tendency of groups to spend disproportionate time and attention on trivial or minor issues while neglecting more significant and complex ones. The term originates from a humorous anecdote in C. Northcote Parkinson’s book “Parkinson’s Law,” published in 1957. The anecdote involves a fictional committee tasked with approving plans for a nuclear power plant. Despite the technical complexity and potential consequences of decisions regarding the power plant’s design and operation, the committee spends a significant amount of time debating trivial matters such as the design and color of a bike shed for the plant’s employees. According to Parkinson, this phenomenon occurs because trivial issues are easier to understand and discuss, leading to more extensive and heated debates compared to complex or technical matters.
The bike-shedding effect highlights several underlying dynamics: Accessibility: Trivial issues are often more accessible and easier to comprehend than complex ones, making them more likely to become the focus of group discussions. Opinions and expertise: Members of a group may feel more confident expressing opinions or providing input on trivial matters, even if they lack expertise in those areas. Desire for participation: People may be more motivated to participate in discussions about trivial matters because they feel their contributions are more likely to be valued or make a difference. Avoidance of complexity: Complex or technical issues may be avoided or deferred because they require more time, effort, and expertise to understand and address effectively. The bike-shedding effect can have implications for group decision-making, project management, and organizational dynamics. It underscores the importance of prioritizing discussions and allocating resources based on the significance and complexity of issues rather than their perceived simplicity or accessibility. Recognizing the bike-shedding effect can help groups and organizations avoid wasting time and energy on trivial matters and focus on addressing more critical challenges and opportunities.
1: Mass of the moving object: [’30: Harmful external factors’]
7: Volume of the moving object: [’30: Harmful external factors’]
9: Speed: [’31: Harmful internal factors’]
10: Force: [’11: Tension, Pressure’, ’13: Stability of the object’, ’17:Temperature’, ’27: Reliability’]
11: Tension, Pressure: [’10: Force’]
13: Stability of the object: [‘1: Mass of the moving object’, ’10: Force’]
15: Action time of the moving object: [’31: Harmful internal factors’]
17:Temperature: [’10: Force’, ’18: Brightness, Visibility’, ’22: Energy loss’, ’23: Material loss’, ’25: Time loss’]
19: Energy consumption of the moving object: [’10: Force’, ’27: Reliability’]
22: Energy loss: [’30: Harmful external factors’, ’31: Harmful internal factors’]
23: Material loss: [’17:Temperature’]
24: Information loss: [’31: Harmful internal factors’]
25: Time loss: [’17:Temperature’]
27: Reliability: [‘9: Speed’, ’19: Energy consumption of the moving object’, ’21: Power’, ’26: Amount of substance’]
30: Harmful external factors: [‘1: Mass of the moving object’, ‘9: Speed’, ’22: Energy loss’]
31: Harmful internal factors: [’16: Action time of the non-moving object’, ’22: Energy loss’, ’24: Information loss’, ’37: Complexity of control and measurement’]
37: Complexity of control and measurement: [’31: Harmful internal factors’, ’38: Level of automation’]
39: Productivity: [’17:Temperature’]
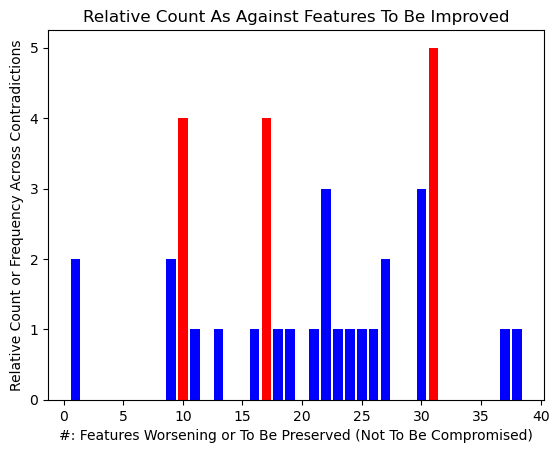
1/30 7/30 9/31 10/11 10/13 10/17 10/27 11/10 13/1 13/10 15/31 17/10 17/18 17/22 17/23 17/25 19/10 19/27 22/30 22/31 23/17 24/31 25/17 27/9 27/19 27/21 27/26 30/1 30/9 30/22 31/16 31/22 31/24 31/37 37/31 37/38 39/17
EXAMPLE: In the context of laptops or PCs, the term “safe mode” typically refers to the Safe Mode provided by the operating system (e.g., Windows). Safe mode is a diagnostic mode that starts the computer with a minimal set of drivers and services. It is designed to troubleshoot and fix problems that might prevent the operating system from starting normally. Safe Mode loads only essential drivers and services, avoiding unnecessary startup programs and components. It can be used to uninstall problematic software, troubleshoot driver issues, or perform system restore. Safe Mode is useful for diagnosing problems during the startup process. If a computer fails to start normally, Safe Mode allows users to troubleshoot the issue.
Contradictions (37/31): 37: Complexity of control and measurement: [’31: Harmful internal factors’, ’38: Level of automation’]
Solution: Safe Mode works by loading a minimal and stable configuration, allowing users to troubleshoot and fix various system-related issues, including driver conflicts, malware removal, and system instability. It loads only essential drivers for basic functionality, and skips or excludes non-essential drivers and startup programs. Generic or default drivers are often used in Safe Mode, bypassing third-party drivers that might be causing conflicts or system instability. Safe Mode prevents most third-party applications and startup items from loading during the boot process. This helps identify if a specific program or driver is causing issues. Safe Mode often uses standard or basic display settings, allowing users to troubleshoot graphics-related problems. Safe Mode helps identify and address issues caused by incompatible or faulty drivers and software. By loading a minimal set of drivers, it allows users to isolate the source of conflicts. Safe Mode is commonly used for malware removal. In Safe Mode, many types of malware and unwanted software are prevented from loading, making it easier to detect and remove them. If the computer experiences frequent crashes or freezes, Safe Mode can help determine whether the issue is related to third-party software or drivers. Safe Mode provides a limited environment for troubleshooting purposes. Once the issues are identified and resolved, the computer can be restarted in normal mode.
Safe Mode allows the computer to boot with a minimal set of drivers and services. By doing so, it helps isolate issues caused by third-party drivers, startup programs, or software conflicts. Malicious software, such as malware and viruses, often relies on specific drivers or services to function. Safe Mode’s limited loading of these components makes it harder for malware to execute harmful actions. Malware may attempt to exploit vulnerabilities in running processes or services. Safe Mode’s focus on stability reduces the likelihood of such exploits. By limiting access to critical system components, Safe Mode reduces the risk of unintended modifications or damage during troubleshooting. This approach helps identify and resolve issues while minimizing the risk of harmful actions, including the execution of malware or the interference of poorly designed third-party components.
Rushing Through + Reverse Action (Time As Transformation) = Going Slow & Steady




